CCNA 4 Final Exam V4.0 2010 |
- CCNA 4 Final Exam V4.0 2010
- Avira AntiVir Premium Security Suite
- McAfee Internet Security 2011
- Eset Smart Security 4.2
- Privacy Alert: 10 Biggest Threats of 2010
- PC Tools Internet Security 2011
- Symantec Norton Internet Security 2011
- Panda Internet Security 2011
- Comodo Internet Security Complete 2011
- F-Secure Internet Security 2011
- BitDefender Internet Security 2011
- Battle of the Security Superpowers
- Webroot Internet Security Essentials 2011
- Security Software: Testing in the Real Wild World
| Posted: 28 Dec 2010 05:20 PM PST 1. What functionality do access control lists provide in the implementation of dynamic NAT on a Cisco router? define which addresses can be translated define which addresses are assigned to a NAT pool define which addresses are allowed out the router define which addresses can be accessed from the inside network 2. Which three guidelines would help contribute to creating a strong password policy? (Choose three.) Once a good password is created, do not change it. Deliberately misspell words when creating passwords. Create passwords that are at least 8 characters in length. Use combinations of upper case, lower case, and special characters. Write passwords in locations that can be easily retrieved to avoid being locked out. Use long words found in the dictionary to make passwords that are easy to remember. 3. Refer to the exhibit. Every time the administrator reboots this router, the boot process ends in setup mode. What is a possible problem? There is insufficient RAM for the IOS to load on this router. A password recovery process should be done on this router. The bootstrap version and the version of the IOS are different. The IOS image is damaged and must be reloaded using tftpdnld. The configuration register is set to ignore the startup configuration. 4. Which option correctly defines the capacity through the local loop guaranteed to a customer by the service provider? BE DE CIR CBIR 5. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from the DHCP server. The output of the debug ip dhcp server command shows "DHCPD: there is no address pool for 10.1.1.1". What is the problem? The 10.1.1.1 address is already configured on Fa0/0. The default router for the 10Network pool is incorrect. The ip helper-address must be added to Fa0/0 interface. The pool of addresses for the 10Network pool is incorrect. 6. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers? ATM Frame Relay HDLC PPP SDLC 7. Refer to the exhibit. Which statement correctly describes how Router1 processes an FTP request that enters interface s0/0/0 and is destined for an FTP server at IP address 192.168.1.5? The router matches the incoming packet to the statement that was created by the access-list 201 deny icmp 192.168.1.0 0.0.0.255 any command, continues comparing the packet to the remaining statements in ACL 201 to ensure that no subsequent statements allow FTP, and then the router drops the packet. The router reaches the end of ACL 101 without matching a condition and drops the packet because there is no statement that was created by the access-list 101 permit ip any any command. The router matches the incoming packet to the statement that was created by the access-list 101 permit ip any 192.168.1.0 0.0.0.255 command and allows the packet into the router. It matches the incoming packet to the statement that was created by the access-list 201 permit ip any any command and allows the packet into the router. 8. Compared with IDS systems, what can IPS systems do to provide further protection of computer systems? detect potential attacks stop the detected attack from executing update OS patches for computer systems scan computer systems for viruses and spyware 9. Which IEEE 802.16 broadband wireless technology allows users to connect to the ISP at speeds comparable to DSL and cable? Wi-Fi satellite WiMAX Metro Ethernet 10. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet? Conduct a performance test and compare with the baseline that was established previously. Interview departmental secretaries and determine if they think load time for web pages has improved. Determine performance on the intranet by monitoring load times of company web pages from remote sites. Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks. 11. Refer to the exhibit. What is the meaning of the term dynamic in the output of the command? The bandwidth capability of the interface increases and decreases automatically based on BECNs. The Serial0/0/1 interface acquired 172.16.3.1 from a DHCP server. The mapping between DLCI 100 and 172.16.3.1 was learned through Inverse ARP. DLCI 100 will automatically adapt to changes in the Frame Relay cloud. 12. Which type of ACL will permit traffic inbound into a private network only if an outbound session has already been established between the source and destination? extended reflexive standard time-based 13. Which two statements are true about IPv6 link local addresses? (Choose two.) They begin with the 2000::/3 prefix. They begin with the FE80::/10 prefix. They are assigned by IANA to an organization. They must be manually configured by the administrator. They are assigned to a host by a stateless autoconfiguration process. 14. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.) reduced jitter reduced costs reduced latency the ability to burst above guaranteed bandwidth the ability to borrow unused bandwidth from the leased lines of other customers 15. Refer to the exhibit. A network administrator is trying to connect R1 remotely to make configuration changes. Based on the exhibited command output, what will be the result when attempting to connect to R1? failure to connect due to Telnet not being enabled failure to connect due to incomplete configuration for Telnet a successful connection and ability to make configuration changes a successful connection but inability to make configuration changes because of the absence of an enable secret password 16. What are two effective measures for securing routers? (Choose two.) Protect all active router interfaces by configuring them as passive interfaces. Configure remote administration through VTY lines for Telnet access. Use quotes or phrases to create pass phrases. Disable the HTTP server service. Enable SNMP traps. 17. An issue of response time has recently arisen on an application server. The new release of a software package has also been installed on the server. The configuration of the network has changed recently. To identify the problem, individuals from both teams responsible for the recent changes begin to investigate the source of the problem. Which statement applies to this situation? Scheduling will be easy if the network and software teams work independently. It will be difficult to isolate the problem if two teams are implementing changes independently. Results from changes will be easier to reconcile and document if each team works in isolation. Only results from the software package should be tested as the network is designed to accommodate the proposed software platform. 18. Refer to the exhibit. From the output of the show interfaces and ping commands, at which layer of the OSI model is a fault indicated? application transport network data link physical 19. Which technology is used to dynamically map next hop, network layer addresses to virtual circuits in a Frame Relay network? Inverse ARP LMI DLCI FECN 20. An administrator learns of an e-mail that has been received by a number of users in the company. This e-mail appears to come from the office of the administrator. The e-mail asks the users to confirm their account and password information. Which type of security threat does this e-mail represent? cracking phishing phreaking spamming 21. Refer to the exhibit. Which data transmission technology is being represented? TDM PPP HDLC SLIP 22. Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2? There is a Layer 2 loop. The VTP domain names do not match. Only one switch can be in server mode. S2 has a higher spanning-tree priority for VLAN 11 than S1 does. 23. What is the result of adding the global command service password-encryption to the configuration of a router? Line passwords are encrypted with type 7 encryption. Enable passwords are encrypted with type 5 encryption. All services must provide an encrypted password to function. Only encrypted messages are allowed for router communication. 24. While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows "up, line protocol up". The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found? application layer network layer data link layer physical layer 25. Where does a service provider assume responsibility from a customer for a WAN connection? local loop DTE cable on router demarcation point demilitarized zone 26. What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server? Traffic that is destined for 192.168.24.1 and 192.168.24.5 will be dropped by the router. Traffic will not be routed from clients with addresses between 192.168.24.1 and 192.168.24.5. The DHCP server will not issue the addresses ranging from 192.168.24.1 to 192.168.24.5. The router will ignore all traffic that comes from the DHCP servers with addresses 192.168.24.1 and 192.168.24.5. 27. Refer to the exhibit. Partial results of the show access-lists and show ip interface FastEthernet 0/1 commands for router Router1 are shown. There are no other ACLs in effect. Host A is unable to telnet to host B. Which action will correct the problem but still restrict other traffic between the two networks? Apply the ACL in the inbound direction. Apply the ACL on the FastEthernet 0/0 interface. Reverse the order of the TCP protocol statements in the ACL. Modify the second entry in the list to permit tcp host 172.16.10.10 any eq telnet . 28. Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses? /19 /20 /21 /22 /23 /24 29. Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue? Enable RIP authentication on R2. Issue the ip directed-broadcast command on R2. Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2. Enable CDP on R2 so that the other routers will receive routing updates. 30. Refer to the exhibit. This serial interface is not functioning correctly. Based on the output shown, what is the most likely cause? improper LMI type interface reset PPP negotiation failure unplugged cable 31. Which statement is true about PAP in the authentication of a PPP session? PAP uses a two-way handshake. The password is unique and random. PAP conducts periodic password challenges. PAP uses MD5 hashing to keep the password secure. 32. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem? When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology. Incorrect IPv4 addresses are entered on the router interfaces. RIPng is incompatible with dual-stack technology. IPv4 is incompatible with RIPng. 33. What is tunneling? using digital certificates to ensure that data endpoints are authentic creating a hash to ensure the integrity of data as it traverses a network using alternate paths to avoid access control lists and bypass security measures encapsulating an entire packet within another packet for transmission over a network 34. Which statement is true about NCP? Link termination is the responsibility of NCP. Each network protocol has a corresponding NCP. NCP establishes the initial link between PPP devices. NCP tests the link to ensure that the link quality is sufficient. 35. Refer to the exhibit. A network administrator is creating a prototype to verify the new WAN design. However, the communication between the two routers cannot be established. Based on the output of the commands, what can be done to solve the problem? Replace the serial cable . Replace the WIC on RA. Configure RA with a clock rate command. Issue a no shutdown interface command on RB. 36. Refer to the exhibit. Based on the output as shown, which two statements correctly define how the router will treat Telnet traffic that comes into interface FastEthernet 0/1? (Choose two). Telnet to 172.16.10.0/24 is denied. Telnet to 172.16.20.0/24 is denied. Telnet to 172.16.0.0/24 is permitted. Telnet to 172.16.10.0/24 is permitted. Telnet to 172.16.20.0/24 is permitted. 37. Which Frame Relay flow control mechanism is used to signal routers that they should reduce the flow rate of frames? DE BE CIR FECN CBIR 38. Refer to the exhibit. A network administrator configures a standard access control list on Router1 to prohibit traffic from the 192.168.0.0/24 network from reaching the Internet. The access control list also permits traffic from the 192.168.0.0/24 network to reach the 192.168.1.0/24 network. On which interface and in which direction should the access control list be applied? interface Fa0/0, inbound interface Fa0/0, outbound interface S0/0/0, inbound interface S0/0/0, outbound 39. Which configuration on the vty lines provides the best security measure for network administrators to remotely access the core routers at headquarters? 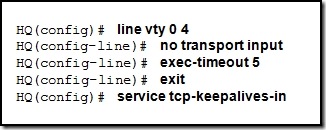 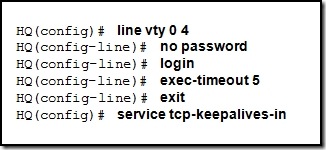 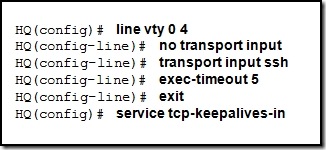 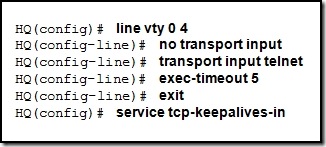 Answer: 3nd option 40. Refer to the exhibit. What can be concluded from the exhibited output of the debug ip nat command? The 10.1.1.225 host is exchanging packets with the 192.168.0.10 host. The native 10.1.200.254 address is being translated to 192.168.0.10. The 192.168.0.0/24 network is the inside network. Port address translation is in effect. 41. A network administrator is instructing a technician on best practices for applying ACLs. Which suggestion should the administrator provide? Named ACLs are less efficient than numbered ACLs. Standard ACLs should be applied closest to the core layer. ACLs applied to outbound interfaces are the most efficient. Extended ACLs should be applied closest to the source that is specified by the ACL. 42. Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices? ATM VPN ISDN Frame Relay broadband DSL 43. Which three physical network problems should be checked when a bottom-up troubleshooting approach has been chosen to troubleshoot network performance? (Choose three.) cable connectivity high collision counts STP failures and loops address mapping errors high CPU utilization rates excess packets that are filtered by the firewall 44. Refer to the exhibit. A network administrator is attempting to configure a Frame Relay network. The administrator enters the commands as shown in the exhibit on R2, but the Frame Relay PVCs are inactive. What is the problem? The incorrect DLCI numbers are being configured on R2. The S0/0/0 interface on R2 needs to be point-to-point. The frame-relay map commands are missing the cisco keyword at the end. A single router interface cannot connect to more than one Frame Relay peer at a time. 45. Which IP address and wildcard mask would be used in an ACL to block traffic from all hosts on the same subnet as host 192.168.16.43/28? access-list 10 deny 192.168.16.0 0.0.0.31 access-list 10 deny 192.168.16.16 0.0.0.31 access-list 10 deny 192.168.16.32 0.0.0.16 access-list 10 deny 192.168.16.32 0.0.0.15 access-list 10 deny 192.168.16.43 0.0.0.16 46. Which combination of Layer 2 protocol and authentication should be used to establish a link without sending authentication information in plain text between a Cisco and a non-Cisco router? PPP with PAP PPP with CHAP HDLC with PAP HDLC with CHAP 47. When would the multipoint keyword be used in Frame Relay PVCs configuration? when global DLCIs are in use when using physical interfaces when multicasts must be supported when participating routers are in the same subnet 48. A network technician analyzes the network and notices late collisions. The collisions occur accompanied by jabber that originates from the server. What is the likely cause of the problem? faulty switch port web server CPU overload faulty NIC in the web server misconfiguration of web server services 49. Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to the web server. What is the destination IP address of the return packet from the web server? 10.1.1.2:1234 172.30.20.1:1234 172.30.20.1:3333 192.168.1.2:80 50. Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem? The default gateway is in the wrong subnet. STP has blocked the port that PC1 is connected to. Port Fa0/2 on S2 is assigned to the wrong VLAN. S2 has the wrong IP address assigned to the VLAN30 interface. 51. When Frame Relay encapsulation is used, what feature provides flow control and exchanges information about the status of virtual circuits? LCP LMI DLCI Inverse ARP 52. A network administrator is tasked with maintaining two remote locations in the same city. Both locations use the same service provider and have the same service plan for DSL service. When comparing download rates, it is noticed that the location on the East side of town has a faster download rate than the location on the West side of town. How can this be explained? The West side has a high volume of POTS traffic. The West side of town is downloading larger packets. The service provider is closer to the location on the East side. More clients share a connection to the DSLAM on the West side. |
| Avira AntiVir Premium Security Suite Posted: 28 Dec 2010 08:00 AM PST |
| Posted: 28 Dec 2010 08:00 AM PST |
| Posted: 28 Dec 2010 08:00 AM PST |
| Privacy Alert: 10 Biggest Threats of 2010 Posted: 28 Dec 2010 08:00 AM PST |
| PC Tools Internet Security 2011 Posted: 28 Dec 2010 08:00 AM PST |
| Symantec Norton Internet Security 2011 Posted: 28 Dec 2010 08:00 AM PST |
| Posted: 28 Dec 2010 08:00 AM PST Let's start with the good news: Panda Internet Security 2011 ($60 for one year, one PC; $70 for one year, three PCs, as of 12/2/2010) has some of the best protection going. Its and 99.8 percent detection of samples of known malware was tops among the 13 applications we tested. It completely blocked 21 of 25 attacks in real-world malware blocking tests (that help determine how well it can block brand new malware), and partially blocked three more, which, while not a top score, is still a solid performance. It's also no slouch in fixing downed machines, removing 80 percent of active malware components. |
| Comodo Internet Security Complete 2011 Posted: 28 Dec 2010 08:00 AM PST |
| F-Secure Internet Security 2011 Posted: 28 Dec 2010 08:00 AM PST |
| BitDefender Internet Security 2011 Posted: 28 Dec 2010 08:00 AM PST |
| Battle of the Security Superpowers Posted: 28 Dec 2010 08:00 AM PST It's no longer enough for antivirus software to scan files on your PC. You need someone looking over your shoulder and telling you whether it's safe to click that link; whether the popup for that software update is legitimate; and whether that download from your favorite social network is actually a tool created by organized criminals for stealing your personal information. You need an all-in-one Internet security suite capable of identifying, blocking, and cleaning up after a wide array of malware. |
| Webroot Internet Security Essentials 2011 Posted: 28 Dec 2010 08:00 AM PST The word "essential" denotes something of absolute necessity--something that you can't get by without. But Webroot Internet Security Essentials 2011 ($60 for one year, three PCs, as of 12/2/2010) is sadly a bit of a misnomer: Its antimalware performance proved it was simply not up to the task of securing a modern PC. If you want "essential" protection, you'll need to look elsewhere. |
| Security Software: Testing in the Real Wild World Posted: 28 Dec 2010 08:00 AM PST |
| You are subscribed to email updates from "Cisco" via Ehsan in Google Reader To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google Inc., 20 West Kinzie, Chicago IL USA 60610 | |












0 comments:
Post a Comment